How To Implement SSL Pinning In Android - Secure Your Android App's Communication
If you're developing an Android application that communicates with a remote server, it's crucial to ensure the data exchanged between the client and server is secure. One way to achieve this is by implementing SSL pinning. Let's learn how to implement SSL pinning in android using OkHttp.
Author:Dr. Felix ChaosphereReviewer:Xander OddityMar 31, 202313 Shares818 Views
If you're developing an Android application that communicates with a remote server, it's crucial to ensure the data exchanged between the client and server is secure. One way to achieve this is by implementing SSL pinning. Let's learn how to implement SSL pinning in androidusing OkHttp.
What Is SSL Pinning, And Why Is It Important?
Secure Sockets Layer (SSL) pinning is a technique used to enhance the security of network communication between a client and server by ensuring that the client only communicates with the intended server and not a malicious one.
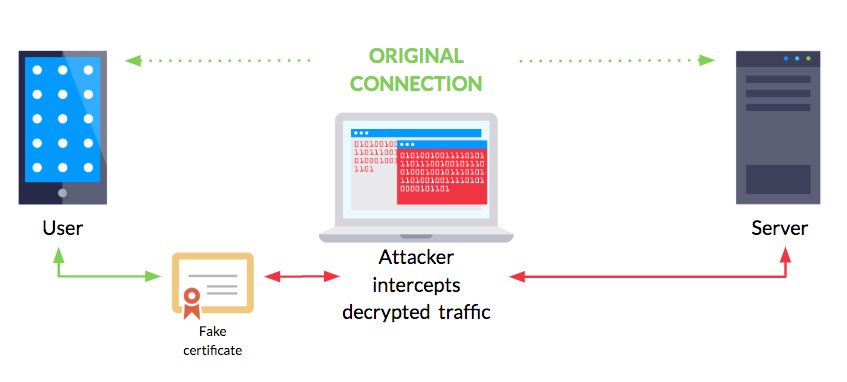
It involves validating the server's SSL certificate against a pre-defined set of trusted certificates or public keys, thereby preventing man-in-the-middle (MITM) attacks.
SSL pinning is important because it helps prevent attackers from intercepting the communication between the client and server and accessing sensitive data, such as login credentials or financial information.
Without SSL pinning, an attacker can impersonate the server and intercept the traffic between the client and server, potentially gaining access to sensitive data or injecting malicious code.
Implementing SSL pinning in your Android app can help prevent such attacks, thereby enhancing the security of your app and protecting the privacy of your users.
How Does SSL Pinning Work?
SSL pinning works by associating a specific SSL certificate or public key with a remote server. When a client initiates a connection to the server, the client verifies that the SSL certificate or public key presented by the server matches the one that the client expects.
If there is a match, the communication proceeds; otherwise, the connection is terminated.
SSL pinning can be implemented in two ways: certificate pinning and public key pinning. In certificate pinning, the client only trusts a specific SSL certificate, whereas, in public key pinning, the client only trusts a specific public key.
Both methods are effective in preventing MITM attacks and can be implemented using popular Android networking libraries like OkHttp.

Android Security SSL Pinning || Codeplayon || Android Tutorial || Android Example
How To Implement SSL Pinning In Android Using OkHttp
OkHttp is a popular HTTP client library for Android apps. It provides a simple interface for making HTTP requests and supports SSL pinning out of the box. Here are the steps to implement SSL pinning in an Android app using OkHttp:
SSL pinning is an important security measure to protect your Android app's communication with servers from Man-in-the-Middle (MitM) attacks. To implement SSL pinning in your Android app, you'll need to follow a few key steps.
First, you'll need to add the OkHttp library to your project's dependencies. OkHttp is a popular HTTP client library for Android that makes it easy to implement SSL pinning.
Next, you'll need to create an instance of the OkHttpClient class with SSL pinning enabled. This involves adding a CertificatePinner to the client instance, which specifies the SSL certificate or public key that should be trusted for a particular domain.
Finally, you can use the OkHttpClient instance to make HTTP requests in your app, just like you would with a regular HTTP client. However, because SSL pinning is enabled, the client will only accept connections from servers with the specified SSL certificate or public key.
By following these steps, you can help ensure that your Android app's communication with servers is secure and protected from MitM attacks. It's important to note that SSL pinning is just one of many security measures that should be implemented in a mobile app to ensure its security.
Tools And Libraries For Implementing SSL Pinning In Android
Implementing SSL pinning in your Android app can be a complex and challenging task. Fortunately, there are many tools and libraries available that can help simplify the process and ensure that your implementation is effective.
Here are some popular tools and libraries that you can use to implement SSL pinning in your Android app:
OkHttp
OkHttp is a popular HTTP client library for Android that provides built-in support for SSL pinning. You can use the CertificatePinner class provided by OkHttp to implement SSL pinning in your app.
TrustKit
TrustKit is an open-source library that provides a simple and easy-to-use interface for implementing SSL pinning in your Android app. It uses a configuration file to specify the domains and pins that should be trusted, making it easy to manage and update SSL pinning values.
Android SSL Pinning Extension
The Android SSL Pinning Extension is a library that provides an easy-to-use interface for implementing SSL pinning in your Android app. It uses a custom TrustManager implementation to enforce SSL pinning and can be easily integrated into your app.
By using these tools and libraries, you can simplify the process of implementing SSL pinning in your Android app and ensure that your implementation is effective and secure.
Common Mistakes To Avoid When Implementing SSL Pinning In Android Apps
Implementing SSL pinning in your Android app can be an effective way to improve its security, but there are several common mistakesthat can compromise the effectiveness of the implementation. Here are some mistakes to avoid:
Using The Wrong SSL Certificate Or Public Key
One of the most important aspects of SSL pinning is using the correct SSL certificate or public key for the domain you're communicating with. If you use the wrong certificate or key, your app may not be able to establish a secure connection. Make sure that you have the correct certificate or key and that it's up-to-date.
Hardcoding SSL Pinning Values
Hardcoding SSL pinning values in your app's code can make it easier for attackers to reverse-engineer your app and discoverthe values.
Instead, consider storing the values in a secure location, such as the app's shared preferences or a backend server. This makes it more difficult for attackers to access the values and helps protect your app's security.
Not Handling Errors Correctly
If there's an error with SSL pinning, such as an invalid certificate or key, it's important to handle the error correction in your app's code. Otherwise, the app may crash or display an error message that could confuse users.
Make sure that your app gracefully handles SSL pinning errors and provides clear and informative error messages to users.
By avoiding these common mistakes, you can help ensure that your SSL pinning implementation is effective and improves the security of your Android app's communication with servers.
People Also Ask
Are There Any Downsides To Implementing SSL Pinning In Android Apps?
One potential downside to implementing SSL pinning in Android apps is that it can make it more difficult to troubleshoot network issues.
Since SSL pinning only allows communication with a specific server, it can prevent the app from communicating with a server that has an invalid or expired SSL certificate. This can result in network errors or unexpected behavior that may be difficult to diagnose.
How Do I Test My SSL Pinning Implementation In My Android App?
To test your SSL pinning implementation, you can use a tool like Charles Proxy or Wireshark to intercept the communication between the client and server.
If your SSL pinning implementation is working correctly, you should see that the app terminates the connection when the server's SSL certificate doesn't match the one embedded within the app.
What Other Security Measures Should I Implement In My Android App?
In addition to SSL pinning, there are several other security measures you should implement in your Android app, such as:
- Implementing secure storage for sensitive data, such as login credentials and financial information
- Encrypting network traffic using HTTPS
- Using authentication and authorization mechanisms to restrict access to sensitive data and functionality
- Enforcing secure coding practices to prevent common vulnerabilities, such as SQL injection and cross-site scripting (XSS)
By implementing these security measures, you can help ensure the overall security of your Android app.
Final Thoughts
Knowing how to implement SSL pinning in Android is an essential step in ensuring the security of your app's network communication. By following the steps outlined in this article, you can implement SSL pinning using the popular OkHttp library.
Remember to test your implementation thoroughly and to implement other security measures to ensure the overall security of your app.

Dr. Felix Chaosphere
Author
Dr. Felix Chaosphere, a renowned and eccentric psychiatrist, is a master of unraveling the complexities of the human mind. With his wild and untamed hair, he embodies the essence of a brilliant but unconventional thinker. As a sexologist, he fearlessly delves into the depths of human desire and intimacy, unearthing hidden truths and challenging societal norms.
Beyond his professional expertise, Dr. Chaosphere is also a celebrated author, renowned for his provocative and thought-provoking literary works. His written words mirror the enigmatic nature of his persona, inviting readers to explore the labyrinthine corridors of the human psyche.
With his indomitable spirit and insatiable curiosity, Dr. Chaosphere continues to push boundaries, challenging society's preconceived notions and inspiring others to embrace their own inner tumult.

Xander Oddity
Reviewer
Xander Oddity, an eccentric and intrepid news reporter, is a master of unearthing the strange and bizarre. With an insatiable curiosity for the unconventional, Xander ventures into the depths of the unknown, fearlessly pursuing stories that defy conventional explanation. Armed with a vast reservoir of knowledge and experience in the realm of conspiracies, Xander is a seasoned investigator of the extraordinary.
Throughout his illustrious career, Xander has built a reputation for delving into the shadows of secrecy and unraveling the enigmatic. With an unyielding determination and an unwavering belief in the power of the bizarre, Xander strives to shed light on the unexplained and challenge the boundaries of conventional wisdom. In his pursuit of the truth, Xander continues to inspire others to question the world around them and embrace the unexpected.
Latest Articles
Popular Articles