Token Grabber Com - The Latest Cybersecurity Threat Explained
A token grabber com is a tool used by hackers to obtain a user's login credentials for various online services. These credentials are typically in the form of authentication tokens, which are temporary keys that grant access to a user's account without requiring them to enter their username and password every time they log in.
Author:Dr. Felix ChaosphereReviewer:Xander OddityMar 08, 202317 Shares574 Views
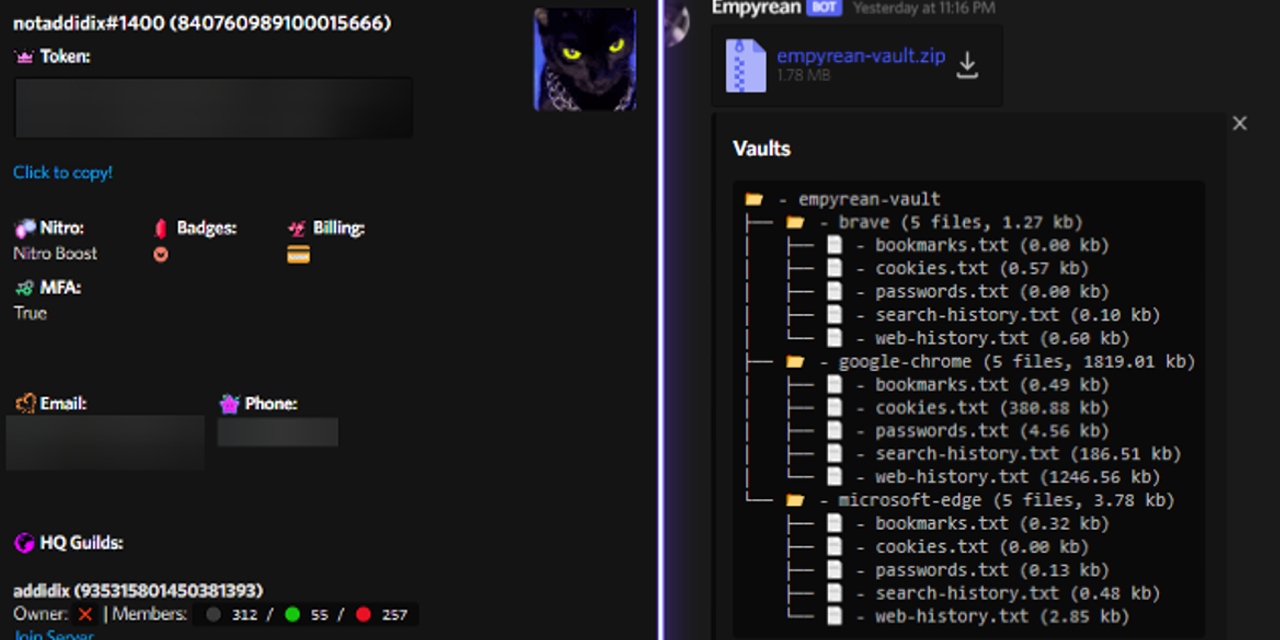
A token grabber comis a tool used by hackers to obtain a user's login credentials for various online services.
These credentials are typically in the form of authentication tokens, which are temporary keys that grant access to a user's account without requiring them to enter their username and password every time they log in.
Token grabbers work by intercepting these tokens as they are transmitted between a user's device and the service's servers.
There are several ways that a token grabber com can be used to steal user credentials. One common method is to use phishing attacks, which involve tricking users into providing their login credentials on a fake website that looks like the legitimate one.
Once the user enters their credentials, the token grabber com intercepts the authentication token and uses it to gain access to the user's account.
Another method of stealingtokens is through malware or viruses that are installed on a user's device. These malicious programs can intercept and steal tokens as they are transmitted between the user's device and the service's servers.
In some cases, the malware may also record the user's keystrokes or take screenshots of their device, which can be used to capture their login credentials directly.
To protect against token grabber com attacks, users should be vigilant about the websites they visit and ensure that they are only entering their credentials on legitimate, secure websites.
They should also use strong, unique passwords for each of their accounts and enable two-factor authentication wherever possible.
Additionally, users should regularly update their software and run antivirus scans to detect and remove any malware or viruses that may be present on their devices.
It is worth noting that token grabber com is not a legitimate or ethical tool. It is often used by hackers or malicious actors to gain access to sensitive information, such as passwords or credit card numbers. The use of token grabber com can lead to severe consequences, such as identity theft or financial fraud.
Token grabber com works by exploiting vulnerabilities in web applications or operating systems to extract tokens, which are used to authenticate users and grant them access to online services.
Once a hacker has obtained a token, they can use it to impersonate the victim and gain access to their accounts and personal information.
To protect oneself from the potential dangers of token grabber com, it is important to practice good cybersecurity hygiene, such as using strong and unique passwords, enabling two-factor authentication, and avoiding suspicious links or downloads. It is also recommended to use reputable security software and to keep it updated regularly.
If you suspect that your accounts or personal information may have been compromised, it is important to take immediate action, such as changing passwords and contacting Token grabber com downloadfinancial institutions or credit reporting agencies to report any suspicious activity.
Video unavailable
This video is unavailable
Is Token Grabber Com Safe?
No, token grabber com is not safe. It is a type of malware designed to steal users' sensitive information, such as login credentials and personal data. It is often distributed through malicious websites, phishing emails, or infected downloads.
Once installed on a device, the token grabber com malware can access and steal user data, which can be used for identity theft or other malicious activities.
It is important to take precautions to avoid downloading or installing any suspicious programs or files, and to keep anti-malware software up to date to protect against these types of threats.
Token grabber com is a type of malware or virus that is designed to steal user tokens, which are digital keys that grant access to online accounts.
When a user logs in to an online account, such as a social media platform or a gaming service, a token is generated to allow the user to stay logged in for a period of time without having to re-enter their credentials.
Token grabber com works by intercepting these tokens and sending them to the attacker's server, allowing the attacker to gain unauthorized access to the user's account.
Token grabber com is typically spread through phishing attacks or malicious links that trick users into downloading and installing the malware.
Once installed, the malware runs in the background, monitoring the user's online activity and looking for tokens to steal. The stolen tokens can then be used by the attacker to access the user's accounts, potentially compromising sensitive personal or financial information.
Users can protect themselves from token grabber com by being cautious of suspicious links or emails and by installing and maintaining up-to-date antivirus software. It is also recommended to use two-factor authentication and to regularly check for unauthorized access to online accounts.
It is important to note that using or downloading token grabber com is illegal and unethical. It is a form of cybercrime that can result in severe consequences, including fines and imprisonment.
People Also Ask
What Is A Token Grabber Com?
A token grabber com is a malicious software that is designed to steal user login information and access tokens.
How Does A Token Grabber Com Work?
A token grabber com works by exploiting vulnerabilities in an application or website to capture access tokens and login credentials of users.
What Are The Risks Of A Token Grabber Com?
A token grabber com can lead to identity theft, unauthorized access to user accounts, and financial loss.
How Can I Protect Myself From A Token Grabber Com?
You can protect yourself from a token grabber com by using strong and unique passwords, enabling two-factor authentication, and keeping your software and antivirus up-to-date.
Can A Token Grabber Com Be Removed?
Yes, a token grabber com can be removed by using antivirus software or malware removal tools.
How Do Hackers Use Stolen Access Tokens?
Hackers use stolen access tokens to gain unauthorized access to user accounts and perform malicious activities such as stealing sensitive data or spreading malware.
Is A Token Grabber Com Illegal?
Yes, creating and distributing a token grabber com is illegal under the Computer Fraud and Abuse Act.
Conclusion
A token grabber com is a tool used by hackers to steal a user's authentication tokens, which can be used to gain access to their online accounts. Users should take precautions to protect themselves against these types of attacks and be cautious about the websites they visit and the credentials they enter online.

Dr. Felix Chaosphere
Author
Dr. Felix Chaosphere, a renowned and eccentric psychiatrist, is a master of unraveling the complexities of the human mind. With his wild and untamed hair, he embodies the essence of a brilliant but unconventional thinker. As a sexologist, he fearlessly delves into the depths of human desire and intimacy, unearthing hidden truths and challenging societal norms.
Beyond his professional expertise, Dr. Chaosphere is also a celebrated author, renowned for his provocative and thought-provoking literary works. His written words mirror the enigmatic nature of his persona, inviting readers to explore the labyrinthine corridors of the human psyche.
With his indomitable spirit and insatiable curiosity, Dr. Chaosphere continues to push boundaries, challenging society's preconceived notions and inspiring others to embrace their own inner tumult.

Xander Oddity
Reviewer
Xander Oddity, an eccentric and intrepid news reporter, is a master of unearthing the strange and bizarre. With an insatiable curiosity for the unconventional, Xander ventures into the depths of the unknown, fearlessly pursuing stories that defy conventional explanation. Armed with a vast reservoir of knowledge and experience in the realm of conspiracies, Xander is a seasoned investigator of the extraordinary.
Throughout his illustrious career, Xander has built a reputation for delving into the shadows of secrecy and unraveling the enigmatic. With an unyielding determination and an unwavering belief in the power of the bizarre, Xander strives to shed light on the unexplained and challenge the boundaries of conventional wisdom. In his pursuit of the truth, Xander continues to inspire others to question the world around them and embrace the unexpected.
Latest Articles
Popular Articles