Trojan Qt5 - What Is This Malicious Malware And How To Protect Your Computer?
With the increasing reliance on technology, the risk of cyberattacks has also increased significantly. One of the most common types of malware is the Trojan virus, and the Trojan Qt5 is no exception.
Author:Xander OddityReviewer:Dr. Felix ChaosphereMar 07, 202317 Shares444 Views
With the increasing reliance on technology, the risk of cyberattacks has also increased significantly. One of the most common types of malware is the Trojan virus, and the Trojan Qt5is no exception. In this article, we will discuss what Trojan Qt5 is, its potential dangers, and how to protect your computer from this virus.
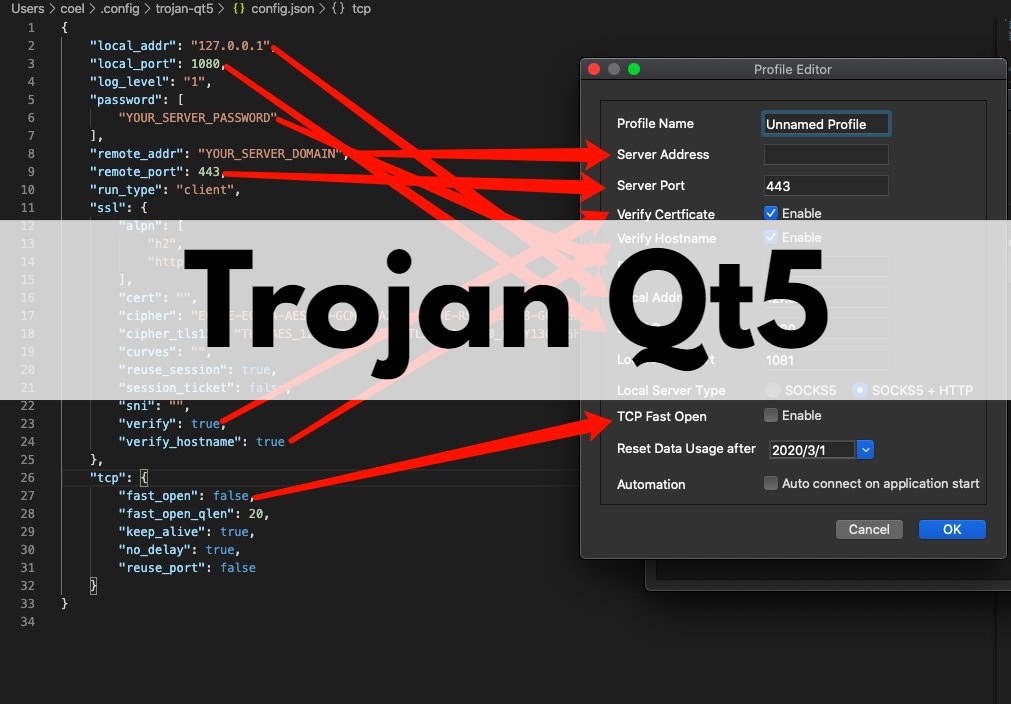
What Is Trojan Qt5?
Trojan Qt5 is a type of Trojan virus that infects computers and gains unauthorized access to sensitive data. It is known for its stealthy nature, which means that it can remain undetected on a computer for a long time.
Once installed on a computer, it can download additional malicious files or even give remote access to hackers, allowing them to control the infected computer.
What Are The Dangers Of Trojan Qt5?
The Trojan Qt5 virus is a serious threat to computer security. It can cause various issues on an infected computer, including:
- Stealingsensitive information: Trojan Qt5 can steal sensitive information such as login credentials, banking information, and other personal data.
- Remote control: Once Trojan Qt5 has established a connection with a remote server, it can give remote access to hackers, allowing them to control the infected computer remotely.
- System crashes: Trojan Qt5 can cause system crashes, making the computer unstable and difficult to use.
- Slower performance: The Trojan Qt5 virus can slow down the performance of the infected computer by consuming system resources.
How Can You Protect Your Computer From Trojan Qt5?
- Install reliable antivirus software -Installing reliable antivirus software can detect and remove the Trojan Qt5 virus from your computer. Antivirus software can also provide real-time protection against future attacks.
- Keep your software up to date - Outdated software can have security vulnerabilities that can be exploited by hackers. Keeping your software up to date can patch these vulnerabilities and prevent Trojan Qt5 from infecting your computer.
- Be cautious when downloading files - Trojan Qt5 can be disguised as a legitimate file, so it's important to be cautious when downloading files from the internet. Avoid downloading files from untrusted sources and always scan downloaded files with antivirus software.
- Use strong passwords -Using strong and unique passwords can prevent Trojan Qt5 from stealing your login credentials. Avoid using easily guessable passwords such as "password" or "123456."
Trojan Qt5 Virus Removal Tools
Trojan Qt5 is a dangerous virus that can cause serious harm to your computer. If you suspect that your computer is infected with this virus, it is important to act quickly to remove it.
There are several virus removal tools available that can help you get rid of Trojan Qt5 and protect your computer from future attacks.
Here are some popular Trojan Qt5 virus removal tools:
- Malwarebytes -Malwarebytes is a popular antivirus software that can detect and remove Trojan Qt5 from your computer. It is easy to use and has a free version that can help you get started.
- Norton - Norton is another popular antivirus software that can help you remove Trojan Qt5. It is known for its powerful malware detection and removal capabilities.
- Kaspersky - Kaspersky is a well-known antivirus software that can detect and remove Trojan Qt5. It is known for its real-time protection and advanced malware removal features.
- McAfee -McAfee is a comprehensive antivirus software that can help you remove Trojan Qt5 and protect your computer from other threats. It offers real-time scanning, automatic updates, and other security features.
- Avast -Avast is a popular antivirus software that can detect and remove Trojan Qt5. It is known for its simple interface and easy-to-use features.
When choosing a Trojan Qt5 virus removal tool, it is important to choose one that is reliable, effective, and easy to use. It is also important to keep your antivirus software updated to ensure that it can detect and remove the latest threats.
In addition to using virus removal tools, there are also other steps you can take to protect your computer from Trojan Qt5 and other viruses. These include:
- Avoiding suspicious websites and downloads -Be cautious when downloading files from the internet and only download files from trusted sources.
- Keeping your software up-to-date - Make sure to install the latest updates for your operating system, web browser, and other software to ensure that you have the latest security features.
- Using strong passwords - Use strong, unique passwords for all of your accounts to prevent hackers from gaining access to your computer and personal information.
- Backing up your data - Make sure to regularly back up your important files and data in case your computer is infected with a virus or suffers a hardware failure.
By using virus removal tools and taking other security measures, you can protect your computer from Trojan Qt5 and other viruses and keep your personal information safe.
People Also Ask
Can Trojan Qt5 Virus Steal Personal Information?
Yes, Trojan Qt5 can be used to steal personal information such as login credentials, credit card numbers, and other sensitive data. It is important to take steps to protect your personal information if you suspect a Trojan Qt5 infection.
How Can I Remove Trojan Qt5 From My Computer?
To remove Trojan Qt5 from your computer, you should run a full system scan with your antivirus software and follow the recommended removal steps. It may also be necessary to manually delete files and registry entries associated with the Trojan.
Is It Possible To Recover Files Damaged By Trojan Qt5?
It may be possible to recover files damaged by Trojan Qt5 using data recovery software or by restoring files from a backup. However, it is important to note that some files may be permanently lost or corrupted.
What Is The Difference Between Trojan Qt5 And Other Types Of Malware?
Trojan Qt5 is a specific type of malware that disguises itself as a legitimate program or file, whereas other types of malware may have different methods of infecting a computer system or causing harm.
Can Trojan Qt5 Be Used For Illegal Activities?
Yes, Trojan Qt5 can be used for illegal activities such as stealing personal information, distributing malware, or launching cyberattacks. It is important to report any suspected illegal activities involving Trojan Qt5 to law enforcement authorities.
Conclusion
Trojan Qt5 is a type of malware that is designed to exploit the Qt framework, a popular development tool used for creating graphical user interfaces (GUIs) in software applications. This malware is capable of infecting various operating systems, including Windows, Linux, and macOS, and can cause significant damage to an infected system.
Trojan Qt5 works by exploiting vulnerabilities in the Qt framework, allowing the malware to execute its malicious code on an infected system. Once the malware gains access to a system, it can perform various malicious activities.

Xander Oddity
Author
Xander Oddity, an eccentric and intrepid news reporter, is a master of unearthing the strange and bizarre. With an insatiable curiosity for the unconventional, Xander ventures into the depths of the unknown, fearlessly pursuing stories that defy conventional explanation. Armed with a vast reservoir of knowledge and experience in the realm of conspiracies, Xander is a seasoned investigator of the extraordinary.
Throughout his illustrious career, Xander has built a reputation for delving into the shadows of secrecy and unraveling the enigmatic. With an unyielding determination and an unwavering belief in the power of the bizarre, Xander strives to shed light on the unexplained and challenge the boundaries of conventional wisdom. In his pursuit of the truth, Xander continues to inspire others to question the world around them and embrace the unexpected.

Dr. Felix Chaosphere
Reviewer
Dr. Felix Chaosphere, a renowned and eccentric psychiatrist, is a master of unraveling the complexities of the human mind. With his wild and untamed hair, he embodies the essence of a brilliant but unconventional thinker. As a sexologist, he fearlessly delves into the depths of human desire and intimacy, unearthing hidden truths and challenging societal norms.
Beyond his professional expertise, Dr. Chaosphere is also a celebrated author, renowned for his provocative and thought-provoking literary works. His written words mirror the enigmatic nature of his persona, inviting readers to explore the labyrinthine corridors of the human psyche.
With his indomitable spirit and insatiable curiosity, Dr. Chaosphere continues to push boundaries, challenging society's preconceived notions and inspiring others to embrace their own inner tumult.
Latest Articles
Popular Articles